The 9 Largest Virtual Reality Stocks
Net Utility Design & Development

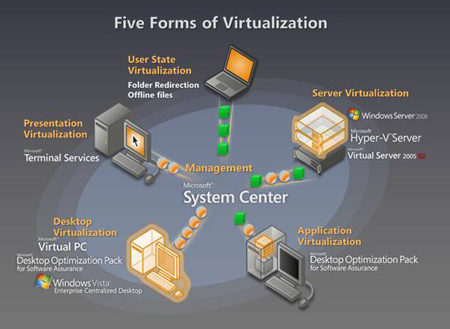
Often the distinctions between APM and UEM definitions are very vendor-particular. Some view UEM as part of APM, while others view it as an adjunct, add-on perform. The vulnerability to theft of a bodily object from a properly secured data middle is more likely to be low. It is troublesome however not impossible to steal a physical server or different substantial hardware resource from a physically secured information center assuming the spectrum of conventional security controls is implemented.
Tech Conferences: The #1 Tech Occasions Information
As Pandemic Lingers, Courts Lean Into Digital Technology
The focus here shall be on VM assault vectors that are facilitated by physical security vulnerabilities or have a bodily part. The level is to point out how bodily security and bodily entry is related to virtualized environments due to the inherent concentration of danger. There are definitely other vulnerabilities inherent to digital environments that should be understood by info security personnel. Perhaps the greatest stress check of digital courtroom know-how occurred in November, when an election law case in Williamsport, Pennsylvania, attracted nationwide attention. When Pechman began to draft a guide for judges and legal professionals on digital bench trials, Chief Judge Richard Martinez requested her to broaden her focus to include digital jury trials, during which jurors would hear the case from house utilizing virtual know-how. The request forced her to contemplate legal and technical questions that literally had no precedent in the federal Judiciary.
Several courts have conducted virtual … Read More